Adding an SSH Key for Your Organization
You can set a private SSH key that Seed will use for all the build processes in your organization. There are a couple of reasons why you might want to do this:
- To check out any additional Git repositories as a part of your build process.
- To run any other operations involving SSH (ie, rsync, ssh, etc.)
To run the above operations you’ll need your private SSH keys in the build process.
Make sure to not store your private SSH keys in your seed.yml or repo.
You can set this by adding a private SSH key for your organization.
Generating an SSH Key
Use the following command to generate your SSH Key.
$ ssh-keygen -m PEM -t rsa -C "your_email@example.com"
Note that, since Seed cannot decrypt SSH keys, every new key must have an empty passphrase. Seed also does not support OpenSSH’s default file format. Make sure to use ssh-keygen -m pem if you are using OpenSSH to generate your key.
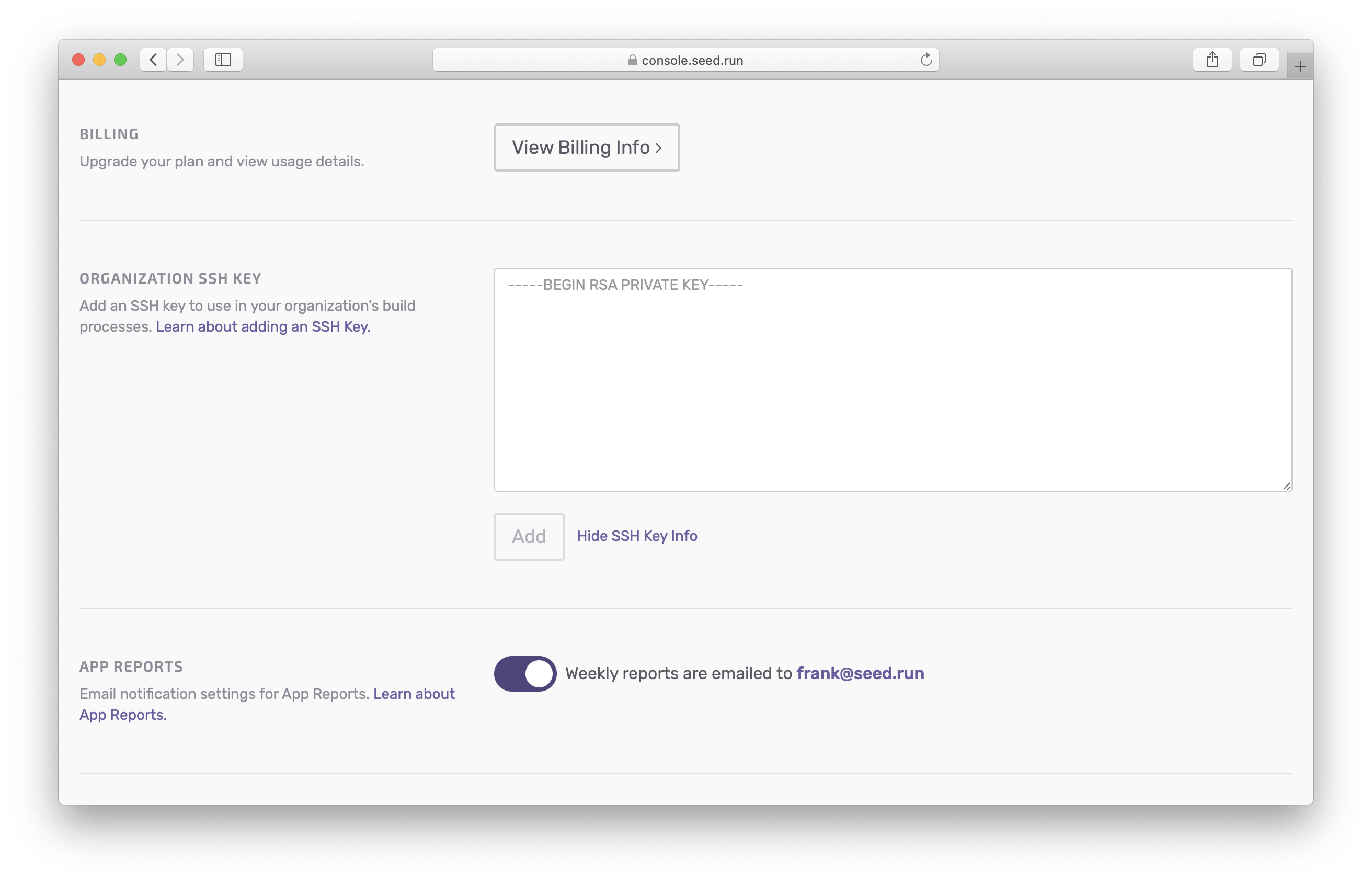
Additionally, recent updates in ssh-keygen don’t generate the key in PEM format by default. If your private key does not start with -----BEGIN RSA PRIVATE KEY-----, enforce PEM format by generating the key with ssh-keygen -m PEM -t rsa -C "your_email@example.com".
Adding an SSH Key
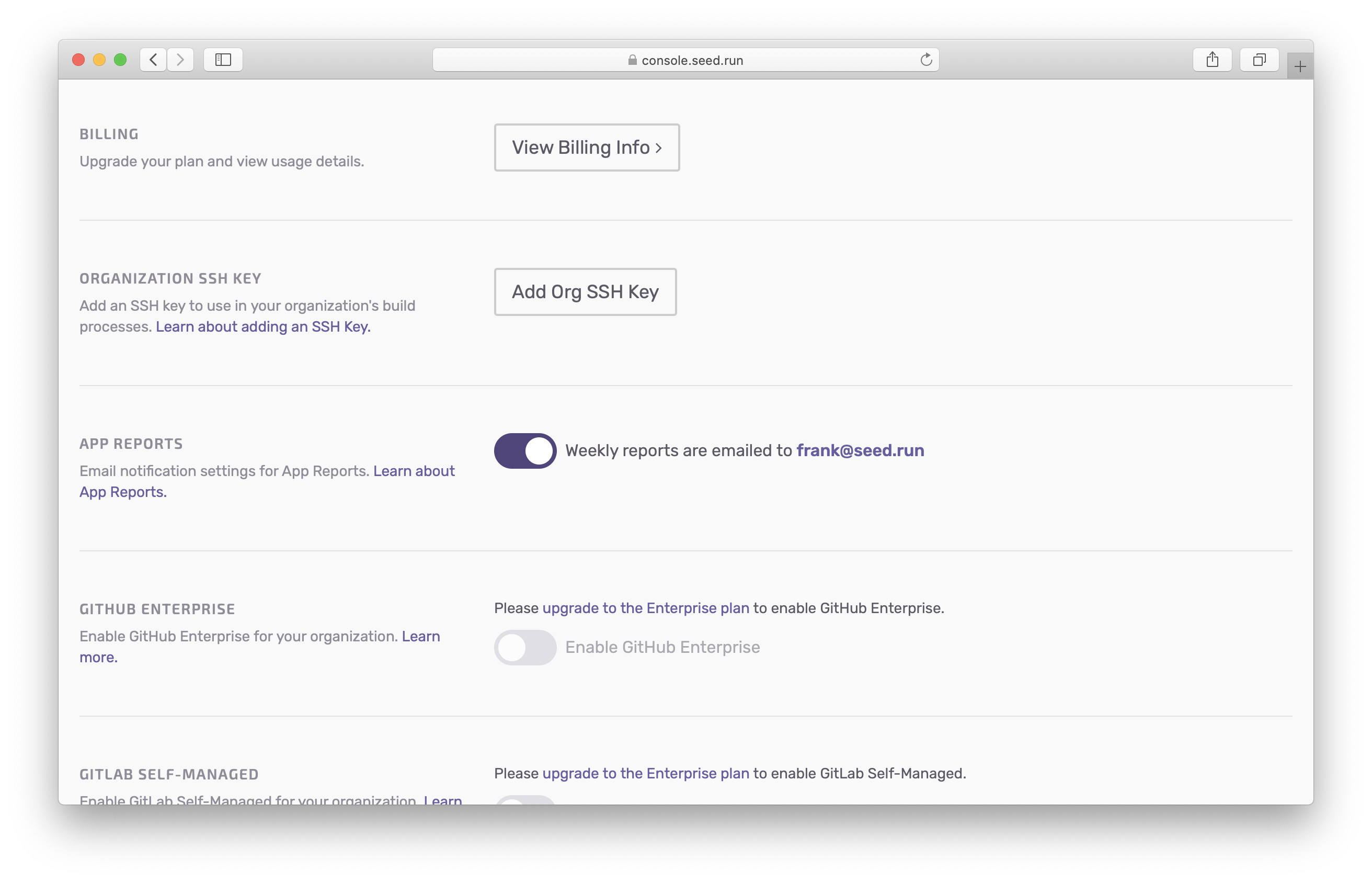
Head over to your organization settings and click on Add Org SSH Key.
Enter your private key and hit Add.
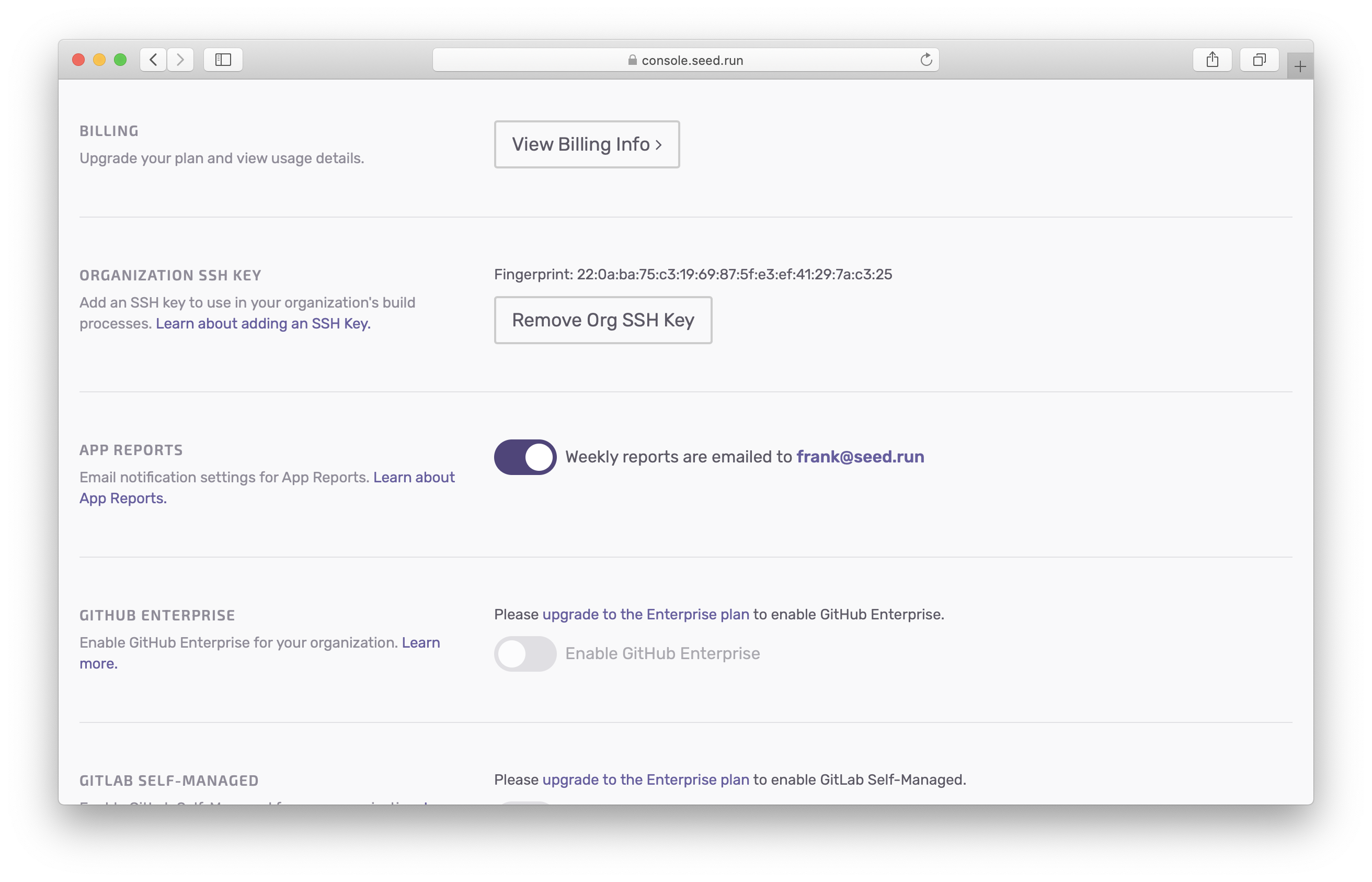
Once it has been added, double check that it has been set correctly by comparing the displayed fingerprint.
Check out Other Repos
If you are looking to check out other repositories as a part of your build process, make sure that you are using the correct SSH URL format:
- GitHub:
git@github.com/... - Bitbucket:
git@bitbucket.org/... - GitLab:
git@gitlab.com/...
Behind the Scenes
Here is what Seed does when an SSH key has been set.
- Takes the private key and writes it to the
~/.ssh/id_rsafile when the build process starts. - Changes the file permissions to
600. - Adds the Git providers domain to the known hosts. Seed uses the same Git provider as the one being used in the build process. For example, if your app is tied to GitHub, then GitHub will be added to the known hosts.
Note that, the SSH key is used in all the build processes for all your apps in your organization.
Help improve this page. Edit it with GitHub
Was this page helpful? Let us know via Twitter
Do your Serverless deployments take too long? Incremental deploys in Seed can speed it up 100x!
Learn More